Introduction
Machine Learning technology has demonstrated tremendous progress over the past few years, thanks to advances in representation learning. As we witness the widespread adoption of these systems, it is imperative to consider the security of such systems. In this project, we explore the incorporation of homomorphic encryption-based solutions within machine learning systems, to prevent information leakage and preserve the privacy of users. A key consideration in employing such solutions is the computational complexity of homomorphic encryption systems. We consider the following problems within this space where we propose solutions to significantly reduce the computational burden of machine learning over encrypted data to make them more practical.
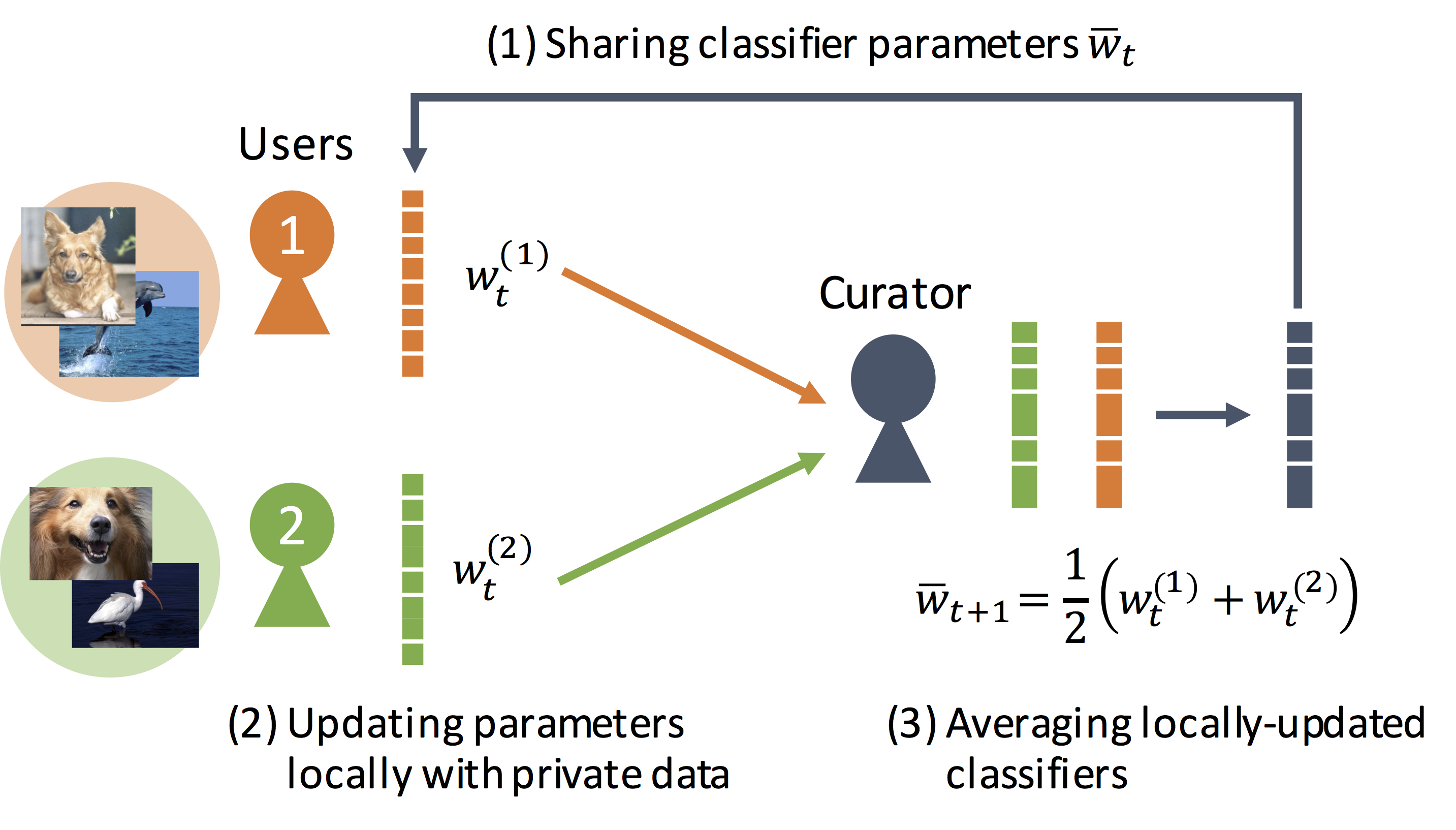
- Federated Learning: How can we leverage large amounts of distributed private for machine learning? We consider a decentralized training system that is designed to aggregate multiple classifiers that are updated locally using private data and to ensure that no private information about the data is exposed during its learning procedure. We utilize a homomorphic cryptosystem that can aggregate the local classifiers while they are encrypted and thus kept secret.
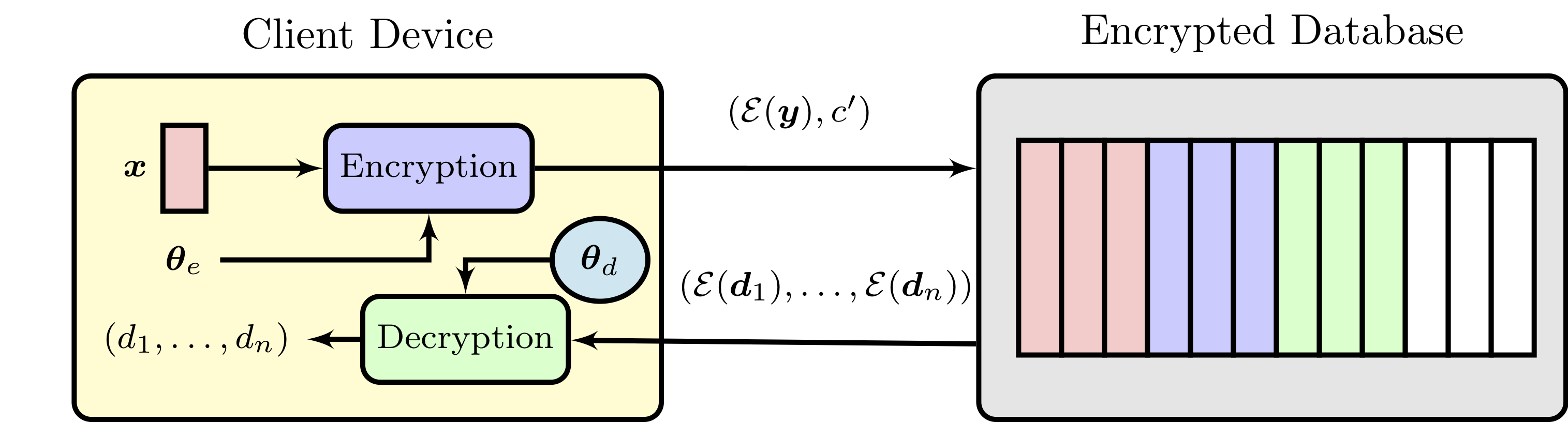
- Secure Face Matching: We explore the possibility of using a fully homomorphic encryption-based scheme for matching face representations directly in the encrypted domain along with a dimensionality reduction scheme to trade-off face matching accuracy and computational complexity.
Contributions
-
A doubly permuted homomorphic encryption scheme for secure and computationally efficient aggregation of multiple classifiers learned from private data.
-
A framework for secure and computationally efficient face matching over an encrypted database. We exploit a batching-based scheme to compute the inner products of encrypted vectors of facial features as well as dimensionality reduction techniques to significantly increase the computational efficiency and practicality of face matching over encrypted data.
References
-
Vishnu Naresh Boddeti, Secure Face Matching Using Fully Homomorphic Encryption BTAS 2018
-
Ryo Yonetani, Vishnu Naresh Boddeti, Kris M. Kitani and Yoichi Sato, Privacy-Preserving Visual Learning Using Doubly Permuted Homomorphic Encryption (Supplementary Material) ICCV 2017